What Is the Pegasus Spyware?
From the dawn of the digital age, cyber security has developed as a new domain of warfare. The lethality and capability of cyber attacks have grown tremendously over the years, and by July 2021, the world experienced a breakthrough in cyber security. through the introduction of the NSO Group’s Pegasus spyware. Although it first emerged in 2016, back then, it was just a phishing software used merely to hack phones by sending the user a text message or a browsing link.
But now, the NSO Group, an Israeli surveillance company, updated it as a “zero-click” malware software that can initiate total surveillance of the targetted device and takes control of one’s entire digital life (Shouvik, 2021). This update in the software created headlines in the international media as a cyber weapon launched to spy on the head of states across the globe.
Despite the allegations of the international media, the NSO Group supported its software and its sales to other governments. Many governments such as India, Saudi Arabia, and the United States of America have been accused of using Pegasus and spying on their arch-rivals, and monitoring the activities of different state and non-state actors.
However, some governments like Pakistan urged the United Nations to investigate the matter after Prime Minister Imran Khan fell victim to the software. For some, Pegasus is a spy that breaches the privacy and national security of the states, but as few governments have already started purchasing it, it may become a requisite for the contemporary security market. Therefore, after the launched updates of Pegasus spyware, a transition in the domain of cyber security and modes of warfare between state and non-state actors is inevitable.
How Does It Work?
The NSO Group’s Pegasus spyware works in three modes: target, infect and track. As far as target is concerned, back in 2016, it used the spear-phishing technique or installed itself through vulnerabilities in smartphone apps but was soon detected the same year when a Mexican journalist fell victim to this spyware after investigating government corruption (Brandom, 2017). However, since 2019, it has become more lethal as it no longer requires any interaction from the owner of the phone.
Individuals may become victims of Pegasus spyware by merely one missed call on WhatsApp through which it installs itself into the phone, and can even delete the record of the missed call, making the owner unaware of the whole situation. After the “target” comes the stage of “infect.” In this mode, the spyware gains access to the phone’s most basic functions and has the authority to copy them.
It can also read through encrypted voicemails and calls, and take over the phone’s camera to record and track your current location. Once the infecting stage is complete, the software moves towards its next and final task, which is to “track.” The software implanted into the victim’s phone activates real-time surveillance without the users’ awareness and reports back to its operator (Chawla, 2021).
Privacy and National Security at Stake!
The turmoil created in international media by this one spyware by Israel makes it more than just a “headline” in our daily newspapers. Albeit the NSO Group claims to use Pegasus only to help government agencies detect and prevent terrorism and crime, other heads of state think otherwise. Moreover, 17 well-reputed media organizations, led by “Forbidden Stories,” a Paris journalism non-profit, disclosed that the mere agenda of Pegasus was to hack the smartphones of high-ranking officials, journalists, and political activists by different governments (Kirchgaessner et al., 2021).
This side of the narrative was upheld by Pakistan and France, as French President Emanuel Macron and Pakistan’s Prime minister Imran Khan fell victim to the spyware attack (Tanvir, 2021). Nonetheless, the NSO Group denies these allegations, claiming that due to the absence of any legal binding, their customers misuse the software for unfair means. “Every allegation about the misuse of the system is concerning me,” Hulio told the Post. “It violates the trust that we give customers. We are investigating every allegation” (Priest et al., 2021).
This statement of the NSO Group seems to be reliable as they blocked Saudi Arabia, Dubai, the United Arab Emirates, and Mexican government agencies from using Pegasus, The Washington Post reported (Dwoskin and Rubin 2021). But the claims of the NSO Group fell over deaf ears when a list of over 50,000 phone numbers of people who might bear significance to NSO clients was provided to 17 news companies by Forbidden Stories and a human rights organization – Amnesty International (Salvador, 2022).
Emmanuel Macron of France, Barham Salih of Iraq, Pakistan’s Imran Khan, Egypt’s Mostafa Madbouly, Morocco’s Saad-Eddine El Othmani, King Mohammed VI of Morocco, and Cyril Ramaphosa of South Africa—all heads of states—are among the 50,000 phone numbers on the rundown. After this revelation, Israel was accused of denying its spying activities and violating the national security borderlines of the states.
In response, the US cut off the NSO Group as a customer of US products and The Commerce Department reported that these tools enabled foreign governments to conduct transnational repression. However, NSO strongly challenged any link to the list of phone numbers. “There is no link between the 50,000 numbers to NSO Group or Pegasus,” the company countered in a statement.
Furthermore, they continued that it was “based on a misleading interpretation of leaked data.” Pegasus “cannot be used to conduct cyber surveillance within the United States,” the company added. The company further explained that it will try to reverse the US government’s sanction. “We look forward to presenting the full information regarding how we have the world’s most rigorous compliance and human rights programs that are based on the American values we deeply share, which already resulted in multiple terminations of contacts with government agencies that misused our products,” an NSO spokesperson said (Priest et al., 2021).
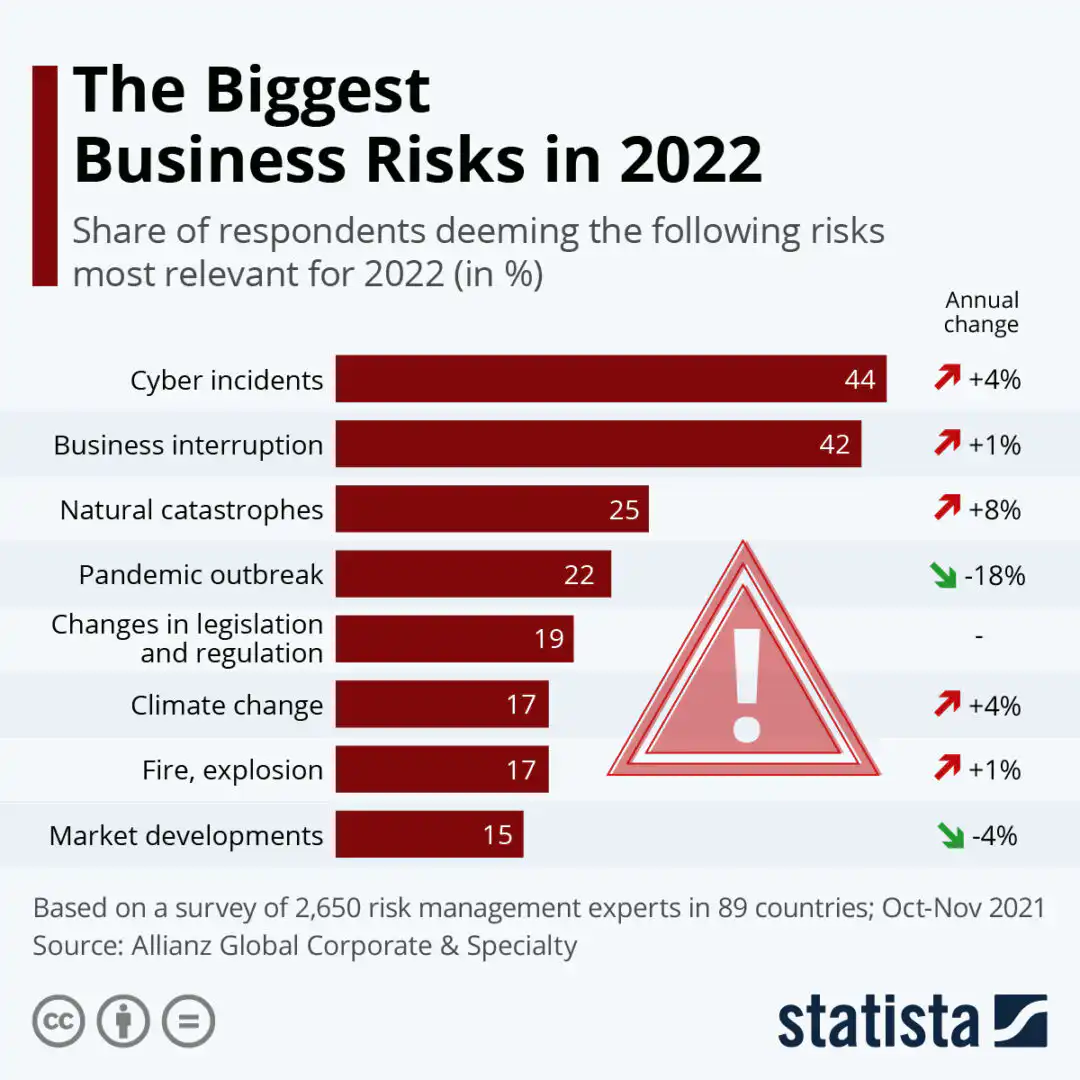
However, despite all the reassurances from the NSO Group, governments across the globe are still subject to agitation as they perceive Pegasus, a cyber weapon, as the greatest threat to their privacy. Online attacks like Pegasus have the potential to jeopardize national security. All the data from the phones of politicians, activists, or heads of states, as mentioned before, can be retrieved by NSO engineers, or it may even lead to worse outcomes if handled by someone with nefarious motives.
Although, when considering the mission statement of NSO Groups’ flagship product, Pegasus, the governments and law enforcement agencies can use this software to maintain national security by intercepting electronic communications to prevent or detect crimes and stave off threats. However, it is critical to understand that fortifying individuals’ privacy may also benefit national security as an unfettered collection of personal data can disclose crucial information about people’s attitudes, sentiments, ideologies, and beliefs.
In the hands of an adversary, such data may be used to influence public behavior and create societal unrest and disharmony. It might likewise be availed to propel an ideological agenda. Similarly, as banking and monetary frameworks are progressively digitized and associated with the web, in this manner, thus that information can be accessed via illicit means. This would eventually affect the states’ economy as, out of fear, people would start withdrawing their resources connected to the internet, banking, or e-commerce.
Violation of cyber security isn’t just a threat to national security paradigms but is likewise hazardous for the escalation of nuclear proliferation. In the contemporary world, cyber weapons are enough to disarm the country from its nuclear weapons and cripple the country’s crucial command and communications capabilities and control. Pegasus has that ability.
This may provide states with the incentive to build additional powerful and lethal nuclear weapons. Thus, one nation that enhances the lethality of its nuclear weapons would be minacious for the national security of its adversary. Therefore, infringement of cyber security borderlines would prompt insecurities among nations as the beneficiary of such an assault may fear more follow-up dynamic assaults, perhaps including the usage of nuclear weapons and, dreading the lack of its ordnance, dispatch its weapons immediately.
A New Demand in the Security Market?
Mexico
Although the uproar in international media painted NSO Group’s Pegasus spyware as a villain of the cyber security realm, to keep up with the pace of the transition in the modes of warfare, many governments purchased the software from Israel’s Ministry of Defense. Mexico is said to be one of the first countries to purchase Pegasus back in 2011 as it helped the Mexican government in Guzman’s capture (Bergman, 2019).
However, it sent shockwaves across global media in 2021 when Mexican journalists like Marcela Turati and 25 others claimed to be spied on by Pegasus (Pieper, 2021). It has been utilized to intimidate journalists and reprimand the movements of activists.
The United States of America
Similarly, it was reported that the United States of America and the Federal Bureau of Investigation (FBI) had secretly purchased the Pegasus software in 2019. As previously NSO Group has claimed that the software could not conduct cyber surveillance in the United States, Pegasus was sold to the FBI with an additional tool that could hack American phones. But it created problems between the FBI and the NSO group when it was reported that at least 11 iPhones used by US officials in Uganda had fallen victim to the spyware (Bing and Menn, 2021).
Therefore, this hack showed crevices present in the software that allowed foreign governments to spy on US citizens and government employees. It was the first incident of technology used against America; however, the identity of the client remains unknown. This reportedly prompted conversations between the FBI and the United States Department of Justice. As a result, the FBI finally opted not to use it, as well as any other NSO malware, in 2021. However, despite ruling against using it, Pegasus equipment is still in the FBI’s possession at a New Jersey facility (Levenson, 2022).

India
India also purchased from Israel, back in 2017, as part of a 2-million-dollar defense deal (Kaushik, 2022). The rundown shared by Forbidden Stories revealed that more than 300 phone numbers belonged to Indian politicians, journalists, and even two incumbent ministers. After this report, the repercussions of the media and people went straight to Indian prime minister Narendra Modi. He was accused of using a foreign country’s malware to spy not just on his primary opponent Rahul Gandhi but also on the Indian security forces, judiciary, opposition leaders, and cabinet members (TRT World, 2021).
Modi and the Bharatiya Janata Party (BJP) have also been accused of targeting Kashmiri Hurriyat (freedom) leaders and Mehbooba Mufti’s family members (The Wire, n.d.). India has also been attempting to establish itself as the hegemon of South Asia by spying on Nepal, Saudi Arabia, Afghanistan, and Bangladesh. Pakistan’s Foreign Office considered this a threat to their national security and condemned these Indian state-supported perpetual and inescapable observation and reconnaissance activities.
It urged the United Nations to divulge into this matter and hold the Indian government responsible. “We condemn in strongest possible terms India’s state-sponsored, continuing and widespread surveillance and spying operations in clear breach of global norms of responsible state behavior,” the ministry said (Khaliq, 2021).
Saudi Arabia & UAE
In December 2020, it was reported that Saudi Arabia and UAE had also purchased the NSO Group’s Pegasus spyware and deployed the exploit against 2 London-based reporters and 36 news-reporter journalists at Al Jazeera in Qatar. Al Araby TV journalist Rania Dridi’s—one of the two London-based journalists—personal iPhone was turned into a spying device at least six times between October 2019 to July 2020 (Berger, 2020). As if spying on journalists was not already an illegitimate act, Crown Prince Muhammad Bin Salman also had the phone of the owner of Amazon, Jeff Bezos, hacked.
In response to the revelation, the NSO Group’s spokesperson claimed that the findings were unreliable and refused to comment on the report, saying that they had not seen the details.
Israel’s Own Use of Pegasus
The NSO Group has warned governments not to abuse the software and has barred nations such as Mexico and the United Arab Emirates. However, it somehow disregards the Israeli government and its abuse of the software. In January 2022, revelations unearthed the use of Pegasus spyware by the Israeli police to eavesdrop on Israeli and foreign citizens who were also infected by the software.
Moreover, it also spied on anti-governmental protesters and activists during Prime Minister Netanyahu’s regime, anti-LGBTQ+ parade activists, and employees of government-owned companies without any warrants or judicial supervision (Ganon, 2022). While featuring their ongoing conflict with Palestine, in October 2021, Israel was also accused of deploying the “zero-click” Pegasus exploits on the devices of Palestinian human rights defenders.
These details were communicated by the Front-line defenders (FLD), a non-governmental human rights association. FLD shared the data with The Citizen Lab and Amnesty International Security Lab and confirmed that six devices were hacked by Pegasus (Jabarin, Hammouri, and Halaika, 2021).
The NSO Group’s Pegasus spyware has slowly but gradually evolved into a desideratum of the new modes of warfare. Despite the backlash faced by Pegasus on global media, it has established itself as a necessity of the contemporary security market as governments from across the globe have acquired it to use it as per their needs. Therefore, one might say that the NSO Group’s Pegasus spyware is officially the need of governments to maintain their security barriers following the cyber security domain and carry out politics across the globe in the name of national interest.
Godfather of the Cybersecurity Realm
A cyber weapon loses its unwavering quality when it is cracked, decoded, and detected by another party. The real question that emerges is whether Pegasus is strong and deadly enough to be considered the godfather of the cyber security realm. The answer is “yes” for a few as the NSO Group claims that it is equipped with a reliable self-destruct mechanism. In general, says NSO, “we understand that it is more important that the source will not be exposed and the target will suspect nothing than keeping the agent alive and working” (Guarnieri, n.d.).
There are a total of 3 scenarios that activate the self-destruct mechanism of Pegasus. Either a threat of disclosure exists or Pegasus doesn’t communicate with its server for over 60 days. The third NSO Group-claimed scenario is when the victim enters the borders of the US, Pegasus goes into self-destruct mode. However, as previously indicated, the third scenario is now a controversial allegation, as the spyware has been identified on American people’s phones as well.
The self-destruct mechanism of the NSO Group’s Pegasus makes it almost impossible to decipher and expose the source, hence, proving it to be the deadliest cyber weapon in the history of warfare. Besides, the self-destruct mechanism, Pegasus also has an invisible transmission system which is why it was able to install itself in iPhones as well.
The sent information is encoded with AES 128-bit symmetric encryption. NSO further explains in its product description report that even during the encryption process, to escape the suspicion of the target, Pegasus keeps a track of the battery, memory, and data of the device and keeps it minimal. NSO also claims that it has put additional effort into compression technologies and focused on textual content transfer whenever feasible to keep data footprints to a few hundred bytes and to have the least possible impact on the target’s phone.
However, data transmission is not possible if the battery runs low and, in such cases, Pegasus keeps the acquired data in a secret and encrypted buffer that is limited to no more than 5% of the device’s free capacity. The correspondence among Pegasus and the focal servers happens through the Pegasus Anonymizing Transmission Network (PATN), which makes following back to the beginning non-plausible.
The way the NSO Group’s Pegasus spyware has sparked outrage over international media and continues to be a hot topic on social media demonstrates that it has caused fear among the nations, the fear of the unknown. It is reasonable to acknowledge that its unrivaled internal mechanism, as well as the dread it instills, has established Pegasus as the best and deadliest spy up till now.
Future of Cybersecurity
In the 21st century, the world has transitioned from full-scale war to cold war and from nuclear weapons to cyber weapons, thus changing the modes of warfare. The world has officially entered the era of hybrid warfare as the production of cyber weapons has surpassed the production of nuclear weapons. Following the disclosure of the NSO Group’s Pegasus spyware, both state and non-state actors and insurgent groups may attempt to avail such spying software to accomplish their objectives.
The utilization of such innovation by antagonist organizations will be disastrous for the world. However, under the given conditions, it appears to be improbable that they would not enhance their combat techniques. Different states, such as China have been using a comparable sort of spyware against their citizens to monitor their daily routines. This is a sheer infringement of fundamental human rights; nevertheless, the conditions portray that such violations may become more common in the future.
Unfortunately, the tendency of eavesdropping on journalists will not abate, rather, it will see an unparalleled spike in the future as the international order undergoes a massive shift under Chinese dominance. This pattern of states meddling with the personal and professional lives of their citizens in the name of cyber security would continue in the future, particularly due to countries such as India and USA which intend to establish themselves as hegemons through cyber surveillance and keep a close watch on their foes.
They constantly strive to keep their actual face hidden, and they manipulate public opinion in their favor through the media. This is only possible if journalists are spied on and forced to do what the state wants one way or another. Henceforth, it is far-fetched that the surveillance of columnists is truly going to stop. Similarly, powerful governments across the world endeavor to crush anti-government leaders, groups, and people demanding autonomy, just as they did in Kashmir and Palestine.
This will also increase government use of spyware software in the future. Governments will also deploy such viruses to impose pressure on other countries. As a result, it is reasonable to predict that espionage applications will become a more effective and crucial instrument of warfare in the future. Finally, cybersecurity defense isn’t going away anytime soon. Organizations will never have a single silver bullet that will completely eradicate the possibility of a cyber attack but will instead have several technologies and processes in place to help ensure such dangers are mitigated.
Conclusion
In light of all the research done on cyber security and Pegasus, it is clear that this is not the end. More noteworthy developments would occur in the near future, prompting the development of more advanced and mechanically enhanced software. The world would now only have to adapt to its different phases of warfare. After all, it is always the survival of the fittest.
References
- Shouvik D. (2021, July 21). Zero click attacks explained: What are they, how do they work. News18.
- Berger, M. (2020, December 20). Report accuses Saudi Arabia, UAE of probably hacking phones of over three dozen journalists in London, Qatar”. The Washington Post. https://www.washingtonpost.com/world/2020/12/20/saudi-arabia-uae-behind-phone-hacks-more-than-three-dozen-journalists-london-qatar-report-finds/
- Bergman, Ronen (January 10, 2019). Exclusive: How Mexican drug baron El Chapo was brought down by technology made in Israel. Ynet
- Bing, C., & Menn, J. (2021, December 4). U.S. state department phones hacked with Israeli company spyware – sources. Reuters.
- Brandom, R. (2017, June 19). Mexican journalist targetted by spyware. The Verge.
- Chawla, A. (2021, July 21). Pegasus Spyware – “A Privacy Killer”. eLibrary.
- Ganon, T. (2022, January 18). Israel police uses NSO’s Pegasus to spy on citizens. CTECH.
- Guarnieri, C. (n.d.). Pegasus – Product Description. NSO Pegasus.
- Jabarin, S., Hammouri, S., & Halaika, G. (2021, November 8). Six Palestinian human rights defenders hacked with NSO group’s Pegasus Spyware. Front Line Defenders.
- Kaushik, K. (2022, January 30). India bought Pegasus as part of defence deal with Israel in 2017: NYT. The Indian Express.
- Kirchgaessner, S., Lewis, P., Pegg, D., Cutler, S., Lakhani, N., & Safi, M. (2021, July 18). Revealed: Leak uncovers global abuse of cyber-surveillance weapon. The Guardian. https://www.theguardian.com/world/2021/jul/18/revealed-leak-uncovers-global-abuse-of-cyber-surveillance-weapon-nso-group-pegasus
- Khaliq, R. (2021, July 23). Pakistan asks UN to hold India accountable over Pegasus spying. Anadolu Ajansı. https://www.aa.com.tr/en/asia-pacific/pakistan-asks-un-to-hold-india-accountable-over-pegasus-spying/2312085
- Levenson, M. (2022, January 28). F.B.I. Secretly bought Israeli Spyware and explored hacking U.S. phones. The New York Times. https://www.nytimes.com/2022/01/28/world/middleeast/israel-pegasus-spyware.html
- Pieper, DW, O. (2021, July 22). Pegasus spyware: Mexico one of the biggest targets. DW. https://www.dw.com/en/pegasus-spyware-mexico-one-of-the-biggest-targets/a-58597847
- Priest, D., Timberg, C., & Mekhennet, E. (2021, July 18). Private Israeli software used to hack cellphones of journalists, activists worldwide. The Washington Post. https://www.washingtonpost.com/investigations/interactive/2021/nso-spyware-pegasus-cellphones/
- Salvador, E. (2022, January 17). Amnesty international verifies use of Pegasus spyware against journalists in El Salvador. Amnesty International.
- Tanvir, M.H. (2021). What is Pegasus spyware and how will it change cyberwarfare? Paradigm Shift. https://www.paradigmshift.com.pk/what-is-pegasus-spyware/
- The Wire. (n.d.). Pegasus project: 174 individuals revealed by the wire on snoop list so far.
- TRT world. (2021, July 21). Modi accused of ‘treason’ as Pegasus spyware row rocks India. Modi accused of ‘treason’ as Pegasus spyware row rocks India.
If you want to submit your articles and/or research papers, please check the Submissions page.
The views and opinions expressed in this article/paper are the author’s own and do not necessarily reflect the editorial position of Paradigm Shift.
Ms. Hamna Binte Waqar is a student of Strategic Studies at National Defence University, Islamabad.